- DCIM?
- What is DCIM?
- What is a Colocation Data Center?
- What is the Federal Data Center Optimization Initiative (DCOI)?
- What is Data Center Management?
- What is Second-Generation DCIM?
- What is Data Center Monitoring?
- What is Data Center Service Management (DCSM)?
- What is Network Documentation?
- What is an Edge Data Center?
- What is a Data Center CMDB?
- What is Data Center Automation?
- How do I get started?
- Products
- Service
- Resources
- Support
- Company
- Search

Security
Safeguard your cabinets against physical threats with DCIM for electronic door locks.
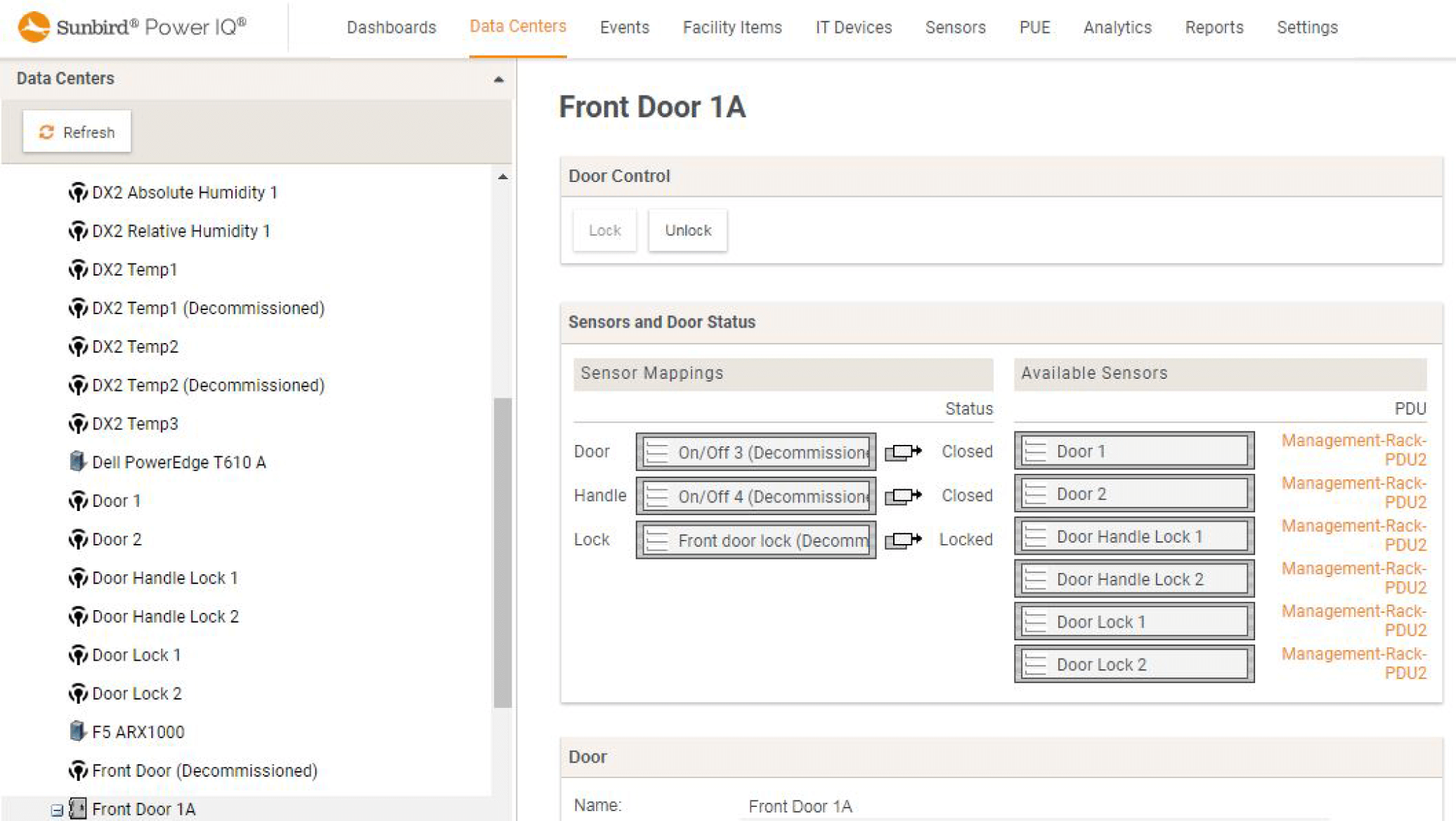

Let authorized users in. Keep intruders out.
Designed to support any locks connected to a Raritan® or CPI® iPDU. This solution can be leveraged in any cabinet, such as those manufactured by Legrand, Ortronics, CPI, Minkels, TANlock, and Afco.

Keep an eye on your data center -
even when you're not on site.
Real-time camera feeds let you view and protect your data centers anytime, anywhere. Our solution works with both IP and USB cameras connected to iPDUs to support plug-and-play functionality that meets your specific security surveillance needs.
Peace of mind for both you and your tenants.
Physical and informational security risks are top of mind for colocation data centers. Ensure that access to company data and customer assets stays in the right hands.
Granular permissions restrict customers access to their own cabinets, data, and reports so you can meet SLA and security requirements
Remote control of doors within the software enables fast, easy, and convenient access and security management from anywhere
Auto-relock timer assures no cabinet will be left unlocked and unprotected
Real-time audit logs and reports ensure compliance with SSAE-16, HIPAA, and other industry-standard regulations
Protect against the biggest enterprise security threat of all: Human error.
Seemingly innocuous employee behaviors can have unintended consequences that compromise the security of your data center. Keep your assets and your employees safe with DCIM software that allows you to:
- Assign and maintain user permissions with granular role-based access control
- Integrate with your existing LDAP, Active Directory, and SAML
- Directory for an additional level of authentication
- Prevent unauthorized access and changes
- Enforce company policies and procedures
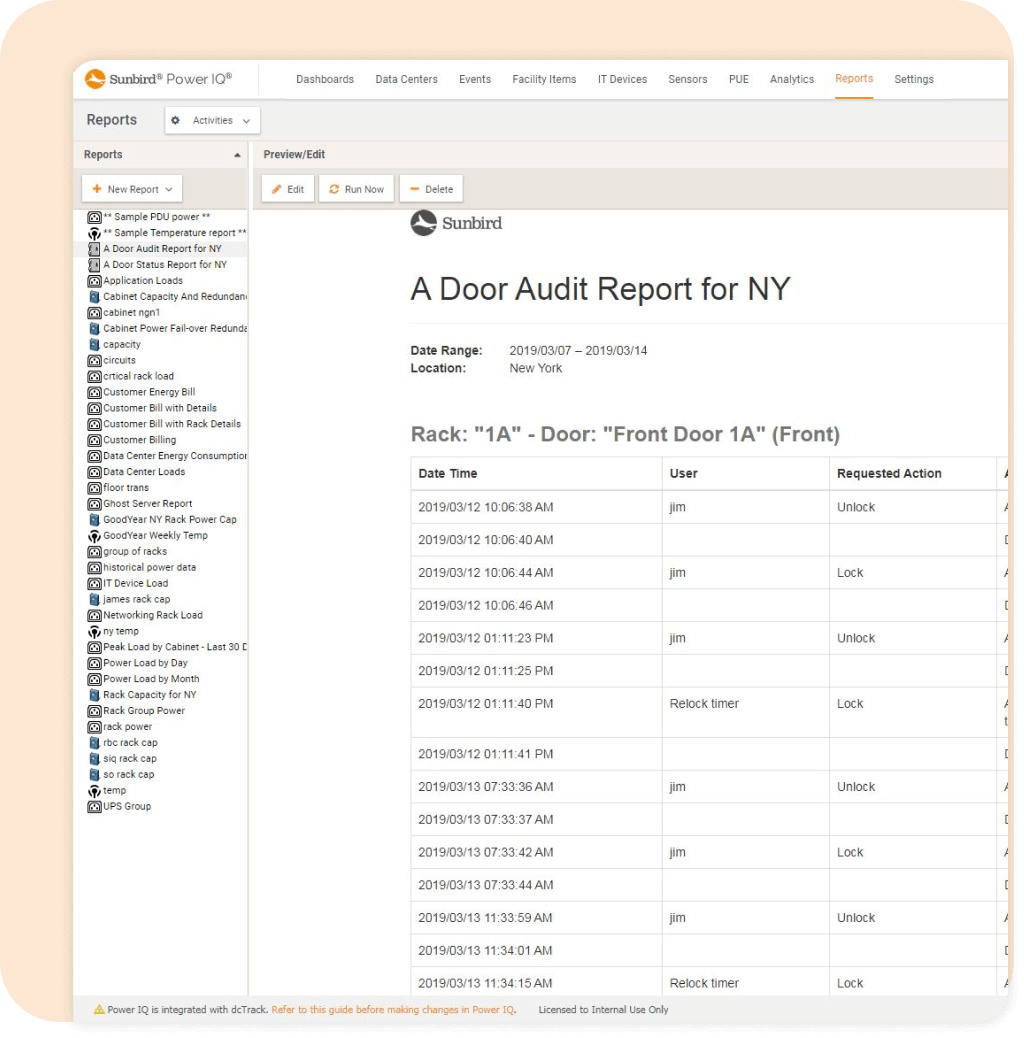
Real-time visibility of audit logs for forensic analysis.
View date- and time-stamped audit log entries for successful user logins, failed logins, remote storage actions, RFID card authorization attempts, and card activations, deactivations, assignments, and updates.
Take the next step with
Sunbird. Try it free.
Test drive remote cabinet security
Log in and remotely control electronic cabinet door locks, restrict access with role-based permissions, and ensure compliance with real-time audit logs.
Try it FreeDownload data sheet
Download the latest data sheet and get the most up-to-date information on our DCIM features.
DownloadSee for yourself with screenshots
View real product screenshots of security to see what it's really like to use Sunbird DCIM.
View Screenshots